Security Operations Centre (SOC) as a strategic security investment

The cyber security threat landscape is changing dramatically. AI-powered phishing attacks, ransomware and advanced persistent threats (APTs) are increasingly bypassing traditional protective measures such as firewalls or antivirus programmes with ease. This dangerous gap between attack and defence not only costs organisations valuable time, but also significant financial resources with every successful cyber attack.
One approach to addressing this challenge is the implementation of a Security Operations Centre (SOC), a central function that combines advanced technology with human expertise. By combining AI-supported behavioural analysis, real-time monitoring and proactive threat detection, a SOC closes precisely those security gaps that cybercriminals would otherwise exploit.
What is a Security Operations Centre (SOC)?
By definition, a Security Operations Centre is a strategic instrument for maintaining cyber security. It combines advanced technologies with experienced analysts in order to detect and defend against potential attacks at an early stage and in real time. The focus of the SOC is on continuous security monitoring and alerting. Around the clock, data from various sources is monitored, unusual events are analysed and immediate countermeasures are taken to protect business processes from serious disruption and to increase the organisation’s security. These comprehensive measures ensure fail-safe and reliable system operation.

Monitoring
Monitoring involves continuously logging customised activities both within the network and on hosts. Tools such as Security Information and Event Management (SIEM) systems enable the collection of log data from various sources such as systems, firewalls, intrusion detection/prevention systems (IDS/IPS), endpoint protection software and network devices.
Detection
To detect anomalies, suspicious activities or potential security incidents, the collected data is analysed in real time. Technologies such as Endpoint Detection and Response (EDR) and Network Detection and Response (NDR) monitor endpoints and networks in real time for suspicious processes, files, traffic or system changes. As soon as these technologies detect an anomaly or potential threat, analysts immediately receive an alert.
Analysis
During the analysis phase, SOC analysts investigate identified security incidents in depth. Particular attention is paid to root cause, scope and potential impact. The SOC analyst evaluates log data, network traffic and system activities in order to determine the method of attack and the vulnerabilities exploited. Using forensic methods and reverse engineering of malware, they attempt to reconstruct the attack scenario and understand which systems or data are affected and whether the attack is still active or has already compromised additional parts of the network. Once the analysis has been completed, the SOC analyst decides on the classification of the incident and the next steps. They determine whether the incident is classified as a true positive and which further measures are required.
Prevention
In cyber security, a distinction is made between a pre-phase and a post-phase of prevention. In the pre-phase, the infrastructure is secured in such a way that threats cannot occur in the first place, for example through the implementation of firewalls, access controls, patch management and regular security reviews. Following an incident, the post-phase takes place, during which preventive measures are implemented to remedy the vulnerabilities that led to the attack. In this way, similar incidents are intended to be avoided in the future.
Response
Once a threat has been detected, immediate measures are taken to limit damage, such as isolating affected systems, blocking compromised accounts, disconnecting affected networks and restoring systems from backups. During the response phase, a detailed forensic investigation is also carried out to determine the attack vector and the extent of the incident. EDR and NDR technologies contribute significantly to the automation and orchestration of threat defence. As a result, threats can be quickly identified, isolated and eliminated without manual intervention. At the same time, activated emergency plans ensure the rapid restoration of operations. After containment of the incident, a lessons learned analysis is conducted in order to better position the organisation for future challenges.
The Security Operations Centre team: roles and responsibilities
The Security Operations Centre (SOC) is designed as a highly modern security control centre in which specialised teams work together seamlessly. The structure follows a carefully developed three-level model that ensures the effective handling of all security aspects. Each level, Security Operations Centre Level 1, Level 2 and Level 3 (also referred to as Tier), includes experts with specific professional expertise and clearly defined areas of responsibility.
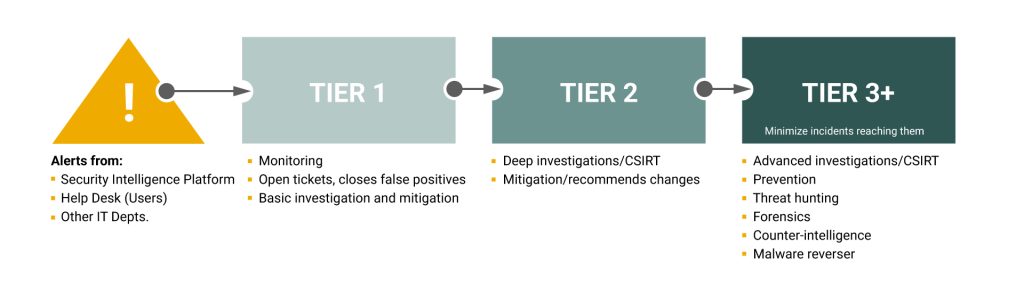
Tier 1 – Triage Analyst
Tier 1 analysts are responsible for recording and performing the initial assessment of security-related events. They analyse alarms and alerts in order to assess and adjust their relevance and criticality. A key component of their work is distinguishing between legitimate alerts (true positives) and false alarms (false positives). They also identify other potential high-risk events, prioritise them according to urgency and escalate unresolved issues to Tier 2 analysts. They often also take responsibility for configuring and managing monitoring tools.
Tier 2 – Incident Responder
Tier 2 analysts are responsible for the in-depth investigation of serious security incidents escalated by Tier 1 specialists. Using threat intelligence, such as indicators of compromise (IOCs) and updated rules, they analyse the extent of an attack and the systems affected. The raw telemetry data from Tier 1 is converted here into actionable threat intelligence. In addition, they develop and implement strategies for containment and recovery following an incident. In the case of particularly complex attacks, they involve additional Tier 2 analysts or escalate the incident to Tier 3.
Tier 3 – Threat Hunter
Tier 3 analysts are the most experienced experts within the Security Operations Centre (SOC). They handle critical incidents escalated by incident responders and conduct vulnerability assessments and penetration tests to identify potential attack vectors. Their primary responsibility is the proactive detection of threats, security gaps and unknown vulnerabilities. In addition, they optimise security monitoring tools and evaluate the security data provided by Tier 1 and Tier 2 analysts in order to ensure comprehensive protective measures.
What are the advantages of a SOC capability for organisations?
- Early detection of threats and continuous monitoring
SOC teams continuously monitor networks, endpoints and applications in real time. This enables potential threats such as malware, phishing attacks or unauthorised access to be detected and mitigated at an early stage. - Rapid response to security incidents
A SOC solution provides clearly defined incident response processes in order to contain attacks quickly and minimise damage. This reduces downtime and protects business operations. - Protection of sensitive data
A Security Operations Centre (SOC) improves the protection of sensitive data, which is particularly important in sectors such as healthcare, financial services and e-commerce. - Cost-efficient security solution
According to a global study, organisations estimate an average budget of approximately USD 2 million for building a SOC, with around one quarter planning more than USD 2.5 million.¹ In addition, ongoing operating costs must be considered. Personnel costs alone for a 24/7 SOC can quickly exceed EUR 1 million per year.² By outsourcing these functions, organisations can reduce substantial upfront investments and long-term operating expenses. - Improved security posture through automation
The integration of technologies such as SIEM and SOAR (Security Orchestration, Automation and Response) enables the automatic prioritisation and analysis of security alerts. - Stronger resilience against cyber attacks
A SOC actively contributes to strengthening cyber resilience by continuously identifying vulnerabilities and proactively implementing measures to close security gaps. - Compliance
A SOC solution supports organisations in meeting regulatory requirements such as the General Data Protection Regulation (GDPR). It can detect and remediate security gaps in real time, thereby supporting compliance with legal requirements and helping to avoid penalties.
Security Operations Centre (SOC) as a cornerstone of cyber security
Within the cyber security threat landscape, a Security Operations Centre represents a fundamental building block of modern organisational defence. The combination of highly qualified experts, advanced technologies and established processes enables 24/7 monitoring, rapid response to security incidents and proactive protection of IT infrastructure. Through the three-tier analysis model, threats are efficiently detected, analysed and mitigated, while automated processes minimise response times and maximise efficiency.
Implementing a SOC solution provides organisations not only with enhanced protection against cyber attacks, but also with significant economic benefits. Compared to an internal SOC, external solutions can deliver substantial cost savings while providing access to highly specialised expertise. The effectiveness of security measures is significantly improved through the integration of modern technologies such as SIEM and SOAR. In the context of increasing compliance requirements and growing cyber threats, a SOC represents an important investment in organisational security.
Contact
Are you looking for an experienced and reliable IT partner?
We offer customised solutions to meet your needs – from consulting, development and integration to operation.
References
- Kaspersky: Costs, timelines and stumbling blocks: what it really takes to build an SOC, 24.02.2026
Costs, timelines and stumbling blocks: what it really takes to build an SOC - IT-Sicherheit.de: Was kostet ein Security Operations Center?, 24.02.2026
Security Operations Center: Kosten
You are currently viewing a placeholder content from HubSpot. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Hubspot Meetings. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information