7P MDM
7P MDM Mobile Threat Defence

100% European protection against mobile threats
Mobile devices act as gateways to critical business and social systems. They process sensitive data, access core applications, and are an integral part of modern working processes. With 7P MDM Mobile Threat Defence powered by Pradeo, we are enhancing our established 7P MDM solution to include powerful Mobile Threat Defence (MTD) functionality. For real-time protection against malware, phishing, network attacks and device compromise.
Why Mobile Threat Defence is essential today
While MDM systems can configure devices, roll out policies and check compliance, there is one thing they cannot do: provide real-time analysis and protection against threats at the application, network and device levels. This is where our solution comes in.
How it works
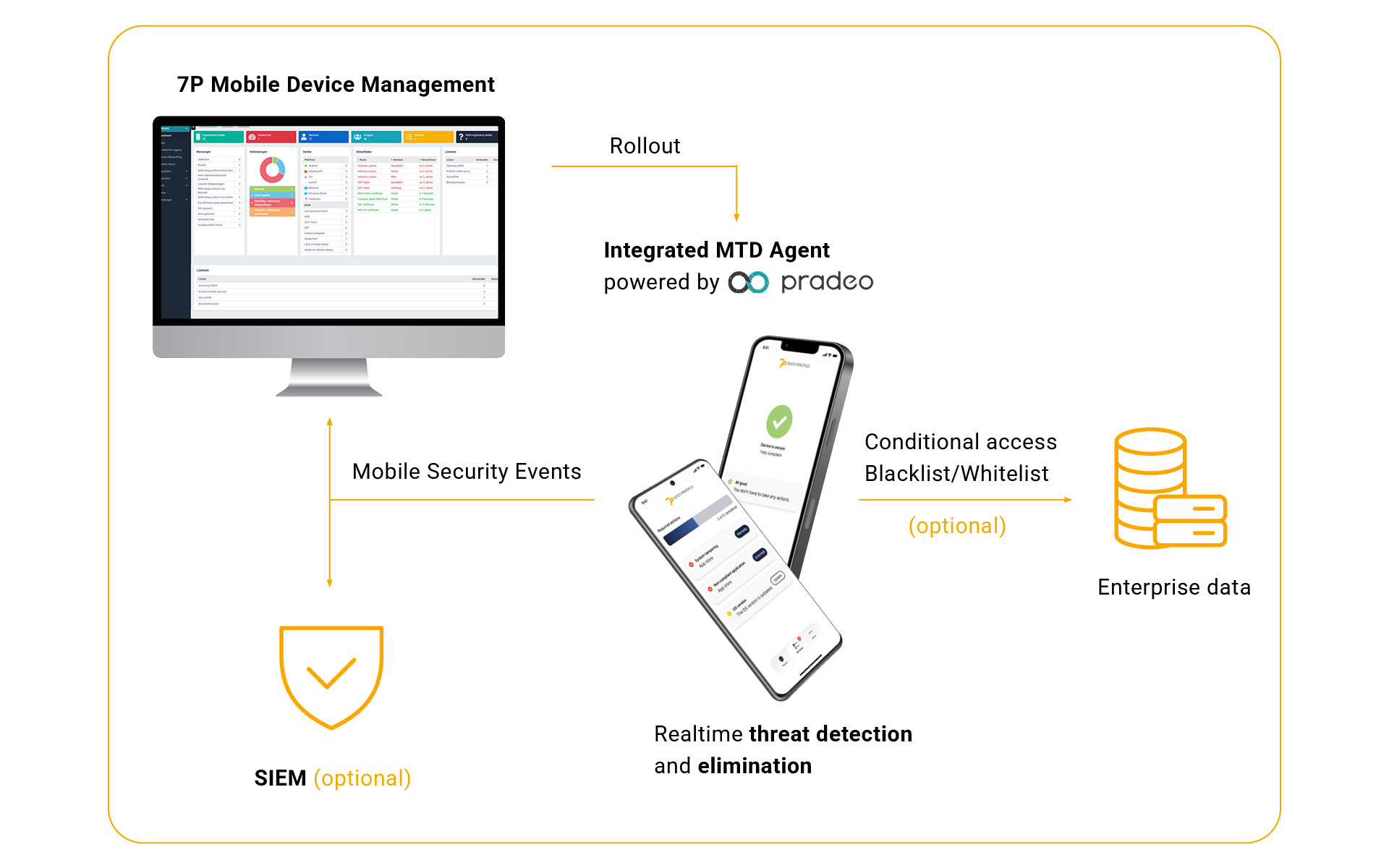
7P MDM Mobile Threat Defence combines our proven 7P Mobile Device Management solution with Pradeo’s leading European mobile threat defence technology, alongside our extensive regulatory expertise and managed services capabilities. The result is a fully integrated security platform that not only manages mobile devices but also actively protects them.
Our technology partnership: 7P & Pradeo
For our Mobile Threat Defence functionality, we have deliberately chosen to rely on the proven technology of our European partner Pradeo, a specialist in mobile security solutions. Pradeo provides the threat detection technology. 7P is responsible for integration, governance and compliance implementation. Through this partnership, we combine specialist mobile security expertise with our many years of experience in regulated industries and secure IT operations.
Your benefits at a glance
Seamless integration with 7P MDM
Deployment is carried out via an integrated Mobile Device Management (MDM) agent, which is automatically rolled out to end devices as part of a zero-touch deployment. Once installed, the agent synchronises with the 7P MDM system, ensuring seamless integration. Security-related events are recorded in real time and displayed on the dashboard, providing a transparent overview of the current security status. Furthermore, the agent enables the implementation of conditional access rules and the enforcement of blacklist and whitelist policies. This creates a holistic security architecture for mobile devices.
Advanced features can significantly broaden the range of applications. For example, integration with SIEM and SOAR systems allows security-related events to be correlated, analysed and processed automatically from a central location. Furthermore, forensic data can be exported in a structured format for further investigation. A multi-tenant architecture enables multiple tenants to operate simultaneously with clear data and configuration separation. Role-based access controls ensure that users can only access the intended functions and information.
Contact
Protect your mobile devices before threats become critical to your business.
Arrange a free initial consultation or book a demo by requesting a no-obligation security assessment now.
FAQ
You are currently viewing a placeholder content from HubSpot. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Hubspot Meetings. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information