Vulnerability and penetration testing for verifiable security
Many organisations do not have a complete overview of which of their systems are externally accessible, and even fewer know which known vulnerabilities in these systems have already been documented but not yet remediated. These gaps are precisely what attackers exploit in a targeted manner. Attacks on critical infrastructures affect organisations of all sizes, across all industries, and often without warning.
The current situation report from the German Federal Office for Information Security (BSI) highlights that the security situation in Germany remains at a tense level.1 On average, 119 new vulnerabilities are recorded worldwide every day, while attack surfaces remain insufficiently protected.2
This leads to a concrete problem. In addition to defending against attacks, gaining transparency over one’s own attack surface is becoming increasingly important. Only when it is clear where vulnerable systems actually exist and how critical they are can risks be meaningfully prioritised and mitigation measures effectively managed. Vulnerability assessments and penetration tests provide this clarity. They systematically examine attack surfaces before a real attacker can exploit them.
What is a vulnerability assessment?
A vulnerability assessment (VA) systematically identifies known vulnerabilities in systems, networks, applications or cloud environments and evaluates them based on their criticality. This results in a reliable overview of all attack vectors, forming the basis for vulnerability management and all subsequent security measures.
The main advantage lies in prioritisation. Security and IT teams gain visibility not only into existing vulnerabilities but also into where to act first. This is particularly valuable when resources are limited and not all findings can be addressed simultaneously.
Core components of a professional vulnerability assessment:
- Automated scanning of IT infrastructure using specialised tools (e.g. Nessus, Qualys, OpenVAS)
- CVE correlation and CVSS-based risk assessment of all findings (Critical, High, Medium, Low)
- Identification of misconfigurations in operating systems, services, network components and cloud environments
- Patch level analysis to detect outdated software versions and missing security updates
- Network segmentation testing to identify unintended communication paths between network zones
- Prioritised reporting with concrete remediation recommendations
When is a vulnerability assessment appropriate?
Vulnerability assessments must be performed regularly as part of continuous vulnerability management. They should also be conducted after significant system changes, such as the introduction of new systems, applications or cloud services, major infrastructure changes or migrations. Other triggers include mergers and acquisitions (IT due diligence) or as a baseline assessment before a penetration test. A re-analysis of vulnerabilities may also be required in the context of compliance requirements (e.g. DORA, NIS2, ISO 27001, BSI IT-Grundschutz).
What a vulnerability assessment does and does not do
Vulnerability tests reveal existing vulnerabilities, but do not show how these can be combined and exploited in a real-world attack.
They provide a fact-based prioritisation, but are no substitute for a manual security assessment carried out by experienced experts. To validate actual exploitability, a penetration test is the appropriate approach.
What is a penetration test?
A penetration test (pentest) verifies whether identified vulnerabilities can actually be exploited and what the resulting impact would be. Qualified IT security experts, often referred to as ethical hackers or red team specialists, simulate targeted attacks on systems, applications or processes. The focus is not only on identifying vulnerabilities but on proving their exploitability and assessing the associated damage potential.
A penetration test shows how far an attacker could get: which vulnerabilities can be combined, how deeply they can penetrate the network, and which data or systems could actually be compromised.
This is the key difference compared to a vulnerability assessment: instead of merely identifying weaknesses, the goal is to understand what an attacker could realistically do with them.
Penetration testing approaches
| Model | Description | Typical use case |
|---|---|---|
| Black Box | No prior knowledge of target systems; attacker acts as an external entity | Simulation of external attackers, realistic scenarios |
| Grey Box | Partial knowledge (e.g. credentials, network diagrams) | Insider scenarios, cloud environments, partner access |
| White Box | Full documentation and source code available | Deep analysis, secure development, code reviews |
Typical scope areas in penetration testing
A penetration test can address various attack vectors. Here are the most common areas of focus:
- External network infrastructure: firewalls, VPNs, exposed services, DMZ components
- Internal networks: lateral movement, privilege escalation, Active Directory attacks
- Web applications and APIs: OWASP Top 10, authentication flaws, injection attacks, business logic flaws
- Mobile applications: iOS and Android apps, local data storage, communication security
- Cloud infrastructure: AWS/Azure/GCP configurations, IAM vulnerabilities, storage permissions
- Social engineering: phishing simulations, vishing, physical tests (red teaming)
Process of a professional penetration test
A pentest follows a defined methodology based on recognised standards (PTES, OWASP, BSI guidelines):
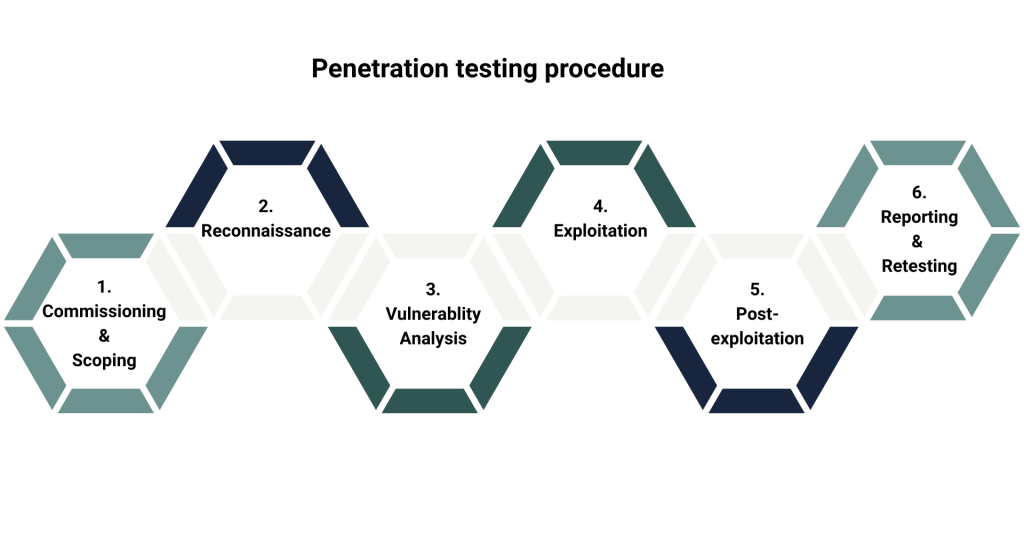
- Scoping and commissioning
Definition of scope, objectives and framework conditions. A formal legal engagement is mandatory. - Reconnaissance
Information gathering (active and passive) and identification of attack surfaces. - Vulnerability analysis
Combined manual and automated analysis of vulnerabilities. - Exploitation
Controlled attempts to exploit vulnerabilities and gain initial access. - Post-exploitation
Analysis of lateral movement, privilege escalation and potential data exfiltration. - Reporting and retesting
Detailed report including executive summary, CVSS-rated findings, remediation recommendations and optional retesting.
Vulnerability assessment vs penetration test
Both methods pursue different objectives. The following overview summarises the key differences.
| Criterion | Vulnerability assessment | Penetration test |
|---|---|---|
| Objective | Identify and prioritise vulnerabilities | Prove exploitability and impact |
| Methodology | Automated scanning and manual analysis | Manual simulation of real attacks |
| Depth | Broad coverage | Deep attack scenarios |
| Frequency | Regular | Event-driven (annually or after changes) |
| Effort | Low to medium | Medium to high |
| Output | Prioritised list of vulnerabilities | Verified attack paths and scenarios |
| Compliance | Basis for vulnerability management | Evidence for NIS2, ISO 27001, PCI DSS, DORA |
Synergistic interaction
A proactive security programme integrates both approaches into a continuous process. Organisations relying solely on regular scans may know their vulnerabilities but not which ones are truly critical in an attack scenario.
Those relying only on penetration tests risk missing newly emerging vulnerabilities between tests.
The recommended approach is continuous vulnerability assessment combined with event-driven penetration testing after major changes, annually, or in line with compliance requirements. Results from both methods should feed into a unified remediation prioritisation process, followed by retesting to validate fixes.
Practical recommendation
Start with a comprehensive vulnerability assessment to establish an up-to-date baseline for your security status. Use the results to prioritise your actions and commission a penetration test that focuses specifically on critical areas and attack vectors. This will maximise the insights you gain whilst optimising the use of resources.
Our services in the field of vulnerability assessment and penetration testing
Regulatory requirements
Frameworks such as NIS2, ISO 27001, DORA, PCI DSS and BSI IT-Grundschutz require organisations to demonstrate that technical security measures are implemented and regularly tested for effectiveness. Failure to provide such evidence can result in fines and loss of trust from customers and regulators.
Both methods deliver documented, reproducible results that can be directly incorporated into compliance reports and audit documentation.
Quality criteria for selecting a provider
The quality of vulnerability assessments (VA) and penetration tests depends largely on the service provider’s expertise. The following criteria are key when making a selection.
- Proven certifications: OSCP, CEH, GPEN, CREST or comparable
- Methodological transparency: use of recognised standards (PTES, OWASP, BSI)
- Clear contractual framework: scope, liability, confidentiality and data handling
- Target audience-oriented reporting: executive summaries for management and technical depth for operations
- Remediation support and retesting
- Industry expertise in regulated sectors
Proactive security requires both approaches
Vulnerability assessments and penetration tests are not competing approaches. Rather, they are complementary pillars of an effective IT security strategy. Vulnerability assessments provide visibility and enable continuous, fact-based vulnerability management. Penetration tests demonstrate the potential actions of attackers.
Combining the two into an ongoing process establishes a robust basis for risk management, credible communication at board level and demonstrable compliance with growing regulatory requirements.
Contact
Are you looking for an experienced and reliable IT partner?
We offer customised solutions to meet your needs – from consulting, development and integration to operation.
Sources
- BSI (2025): Die Lage der IT-Sicherheit in Deutschland 2025 (Zusammenfassung)
BSI – Bundesamt für Sicherheit in der Informationstechnik – Die Lage der IT-Sicherheit in Deutschland 2025 (Zusammenfassung)
Retrieved on 08/04/2026 - BSI (2025): Die Lage der IT-Sicherheit in Deutschland 2025
Die Lage der IT-Sicherheit in Deutschland 2025
Retrieved on 08/04/2026
You are currently viewing a placeholder content from HubSpot. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Hubspot Meetings. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information