Shadow IT in Germany: Managing risks properly
Shadow IT does not originate in the data centre, but within business units. A sales team independently subscribes to a SaaS CRM because the existing system is too slow. The marketing department uses a US-based cloud storage solution because the internal one is too cumbersome. HR turns to a free survey tool to gather feedback quickly. And since generative AI has entered everyday work, confidential text modules and customer data are also being fed into tools like ChatGPT and similar platforms.
All of this constitutes shadow IT and is part of everyday life in German companies.
Anyone who views shadow IT solely as a security issue has not yet grasped the crux of the problem. Shadow IT is a symptom of a mismatch between the requirements of business teams and the solutions provided by the IT department.
This article argues for a shift in perspective. Away from the view of IT as a controlling authority, towards IT as a business enabler through managed shadow IT. It is not necessary to ban and combat everything. Rather, it should be managed and shaped.
What is shadow IT?
Shadow IT refers to tools, applications and IT services used without the approval or knowledge of central IT.
- SaaS and cloud services procured directly by business units.
- Tools paid for using company credit cards or private accounts.
- In-house developments based on Excel, Access or low-code platforms.
- ‘Shadow AI’, i.e. AI tools used with company data outside official processes.
Over time, not only the volume but also the significance has changed. In the past, shadow IT was primarily a concern for administrators and auditors. Today, it is a strategic issue for management. Shadow IT clearly highlights where processes are too slow, standards no longer fit, or IT is too far removed from actual workflows. It is therefore less a sign of rule-breaking than of pressure to act.
The uncomfortable truth: shadow IT is often an act of personal initiative. Employees are trying to solve problems efficiently. Bans alone do not solve the problem. They merely push it further into the shadows.
Why does shadow IT arise?
Shadow IT rarely arises from a deliberate breach of rules, but almost always due to structural tensions between business and IT. In practice, these can be traced back to a few key causes:
- Speed: Projects take months, whereas business units think in weeks.
- Restrictions: Standard toolsets do not adequately cover modern use cases.
- Complexity: Approval processes are opaque or bureaucratic.
- Lack of dialogue: IT is involved too late in business initiatives.
The outcome is predictable. Business departments organise themselves independently and without official processes. Not out of defiance, but due to time pressure. In complex organisations, control no longer works without understanding.
The necessary shift in perspective: IT as a business enabler
Historically, many IT departments are structured like regulatory authorities. They operate infrastructure, secure systems, define standards and minimise risks. This remains important, but is no longer sufficient.
The required shift is obvious. IT no longer needs to build and operate everything itself. Its role is increasingly to curate, integrate and manage solutions. Not every tool needs to be developed in-house. But every relevant tool must be understood, evaluated and properly integrated.
Instead of blanket bans, guardrails are needed. That means clear rules, transparent processes and a shared understanding of acceptable risk. This turns IT from a gatekeeper into a partner that enables speed without compromising security and compliance.
Managed Shadow IT
Completely eliminating shadow IT is neither realistic nor desirable. Modern businesses thrive on experimentation. The crucial question is therefore not how to prevent shadow IT, but rather how to make it manageable.
Managed Shadow IT means that IT accepts that business units evaluate tools independently. At the same time, there are defined processes for reporting, assessing and, if suitable, officially integrating these tools. In practice, this approach is based on four elements:
| 1. Creating transparency | – Establishing a continuous ‘discovery’ process (e.g. by analysing single sign-on, network traffic, expense data, browser plugins). – Regular discussions with business departments: “Which tools are being used officially/unofficially?” |
| 2. Risk classification instead of black-and-white thinking | – Simple categorisation: non-critical, moderately critical, highly critical. – The higher the risk, the greater the requirements for testing and integration. – Low-threshold approvals for low-risk tools, clearly defined testing processes for high-risk tools. |
| 3. Standardised quick assessments | – Short checklists for departments: data type, data storage location, provider, access policy. – IT evaluates based on this information. |
| 4. Governance by design | – Where possible, new tools are integrated via centralised identities (SSO), role and permission concepts, and logging. – Technical safeguards (e.g. DLP, CASB) support policies without stifling innovation. |
‘Shadow AI’ as an invisible threat
Generative AI takes shadow IT to a whole new level. Employees use AI tools for text, translations, code or presentations. What initially appears harmless can quickly become critical when personal data, confidential information or intellectual property is processed.
Typical risks of shadow AI:
- Unintended leakage of know-how into external models
- Breach of internal confidentiality policies
- GDPR risks due to the processing of personal data
- Reputational damage if confidential content ‘leaks’ or is reflected in AI outputs
A general ban on AI is unrealistic. Departments will use AI, with or without authorisation. The more sensible approach is therefore the ‘enabler’ approach. Companies provide vetted AI platforms, clearly define which data may be used, and train their employees using concrete examples. Technical safeguards complement these rules, but do not replace them.
IT amnesty: building trust instead of fear
Many organisations know that more tools are in use than officially recorded. Nevertheless, employees remain silent out of concern about sanctions. This is precisely where the concept of a strategic IT amnesty comes in.
Instead of threatening sanctions, a clearly communicated, time-limited period is announced during which the following applies: “Anything you report now will not result in disciplinary action. Our aim is transparency, not punishment.”
Within a clearly defined timeframe, it is openly communicated that reported tools will not result in disciplinary consequences. The aim is transparency, not punishment. Prerequisites include a clear message from executive management and IT, simple reporting mechanisms and a visible willingness to act on the insights gained.
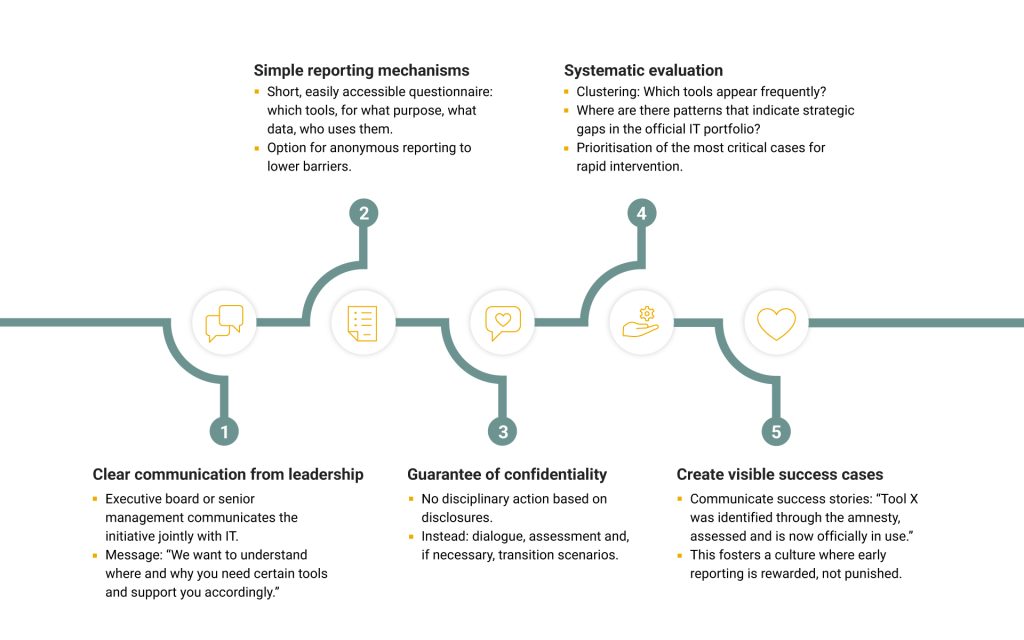
When reported shadow IT becomes validated, officially usable solutions, trust emerges. And trust is the foundation of any functioning governance.
Compliance and GDPR: The risk of unknown server locations
In German and European companies, shadow IT represents a liability risk. The critical issue lies less in the individual tools than in the lack of transparency: it is unclear where data is processed, on which servers it is stored, and which data processors are involved.
This is particularly problematic in the context of the GDPR. Typical everyday scenarios range from US-based survey tools in HR to free CRM solutions from unknown providers, to the use of external AI services for contracts, customer data or internal documents. It is often unclear whether this involves permissible data processing or uncontrolled transfers to third countries.
This lack of transparency becomes a problem at the latest during audits, data protection enquiries or security incidents. Key questions cannot be answered with certainty: Where is the data stored? Who is processing it? On what legal basis? In cases of gross negligence, this can extend to personal liability for executive management. As a result, shadow IT transforms from an operational nuisance into a board-level risk.
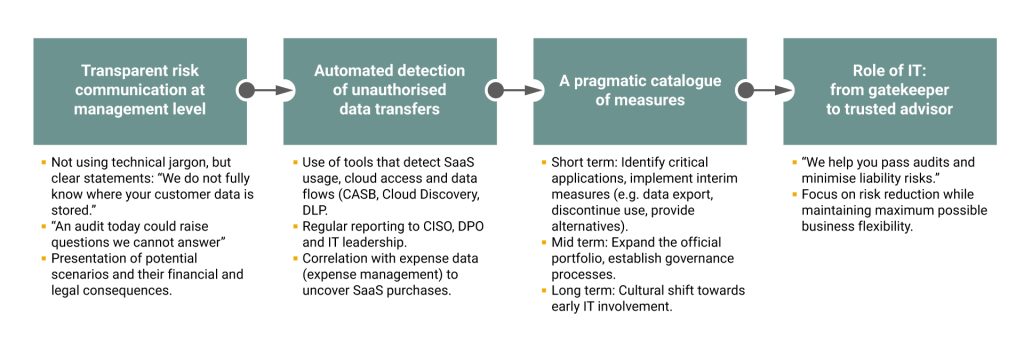
IT as a service broker instead of operator
If this approach is followed consistently, IT becomes a platform. It no longer operates everything itself, but orchestrates internal and external services. Business units access verified tools via self-service portals. Security, compliance and quality requirements are transparently defined. In this model, managed shadow IT becomes the norm. IT creates a framework in which innovation remains possible without leaving security and compliance to chance.
Central self-service portal (corporate app store)
In the target scenario, business units no longer access tools via informal workarounds, but use a central self-service portal. This company-wide app store bundles internal and external applications that have been technically, legally and organisationally validated. For each solution, it is clearly documented what it is approved for, where data is processed and who is responsible on the business side.
Modular architecture and integration standards
To prevent new tools from emerging in isolation, IT relies on clear integration standards. Applications are connected via APIs, SSO, centralised identities and consistent role models. Data flows are documented and access is traceable. This reduces dependencies and facilitates the exchange of components.
Clear governance with role concept
The service broker role defines security standards, minimum requirements and certifications. Within these guardrails, business units can independently decide which tools to use. The Risk, Compliance and Data Protection departments become co-designers of the platform.
Continuous portfolio optimisation
A curated service ecosystem is not a static state. The usage, added value and risks of the tools in use are regularly reviewed. Redundant solutions are consolidated and successful approaches scaled up. New shadow IT, which becomes visible through discovery, can be specifically transferred to the official portfolio if it offers business value.
Shadow IT as a strategic opportunity
As long as people try to solve problems efficiently, shadow IT will persist. The traditional response in the form of bans and blocks may provide short-term reassurance, but is dangerous in the long term. It increases intransparency, exacerbates liability risks and deprives management of the basis for informed decision-making.
The solution to this problem is more demanding. It requires the courage to embrace change, trust in the business units, and an IT department that consciously positions itself as an enabler. Managed shadow IT, clear guidelines, confident handling of shadow AI, and an open governance culture are all signs of leadership maturity.
This is precisely where digital leadership begins. Not with the introduction of new tools, but rather where responsibility for speed, security and compliance is conceived jointly. Companies that view shadow IT as a feedback channel and actively shape it transform their IT from a controlling body into a strategic partner.
The crucial question is therefore not how to prevent shadow IT, but how it can be used to lead the company better, faster and more resiliently, with an IT department that not only claims digital leadership, but lives it.
Contact
Are you looking for an experienced and reliable IT partner?
We offer customised solutions to meet your needs – from consulting, development and integration to operation.
You are currently viewing a placeholder content from HubSpot. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Hubspot Meetings. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information